|
| HOME | SOLUTIONS | DOWNLOAD | SUPPORT | PURCHASE | COMPANY |
| Home » Solutions » ICE License |
Overview
The strongest and most complete protection available today for Borland Delphi and C++ Builder. ICE License is a new and innovative licensing protection system for Borland developers wishing to integrate copy protection and maximum security into their applications. Professional Copy Protection for Borland ICE License is designed for Borland Delphi (from Delphi 5 up to 2007) and C++ Builder, add VCL copy protection system on your projects and get a high level of security. Some protections don't work in entreprise environment, because user's account is limited or restricted and require administrator rights to run application, so you lose many customers becaue they can't try your evaluation version.With ICE License you can protect your application, run in restricted environment without requiring administrator right, it's difference than other protection. With ICE License it's easy to turn your application into "try-before-you-buy" versions with little effort, offering everything to guarantee maximum protection. If you want to protect your investments, ICE License is designed specifically for you. ICE License has been created for the software developer looking for powerful and flexible protection, license management tools and to retain total control of their software products when delivering them into the hands of their customers. Build Multi-Editions in One Building one product version and using digital licensing to partition that product through license-based feature access controls reduces the need for distinct product upgrades and saves engineering and quality assurance costs. ICE License Protection can help you prevent key generation and therefore help to protect your investment. Our Protection Technology Antidebugging protection to prevent reverse engineering ICE License use antidebugging and antimonitoring protect which provide a good way to prevent people from analysing your code instructions. Asymmetric encryption technology to prevent against key generator ICE License Protection provides a high barrier against illegal copy using the power of asymmetric encryption to protect your application. The asymmetric encryption system allows for the transmission of secret information over an open channel without a common secret key previously shared between the ends of the transmission. Your application is protected by two keys; One key (public key) is inside your application and the second is a private key known only to the developer. These two keys are used in combination to encrypt and decrypt the software Key. Even if cracker can access to the source of ICE License, he cannot make key generator, due to the Asymmetric Encryption (based on public key asymmetric) systems, example : RSA Encryption, the source is available on the net, but it's very hard to break. Only you can control the software license creation so that no key generator can be made. Runtime Source Code Encryption to prevent against patching or cracking Fragments of code are marked in your source code by using special start and end marks. These fragments of code are recognized by ICE License in the compiled application and are additionally encrypted during the protection process. Runtime encrypted code always stays encrypted in memory. It's managed by special code each time it should be executed. Due to the encrypted blocks inside your software, your program cannot be completely cracked without a real key. This ActiveKey can be provided only in the Full License Key. If cracker try to patch your application to avoid control, he cannot crack (to turn in full) your software, because inside your compiled executable, the key for decryption is not inside, it's different approach than other protection. Secure application strings resource using encryption With the SecureStrings feature, you can encrypt all strings in your application. SecureStrings encrypt and decrypt in memory to protect them from being viewed or changed by anyone other than developer. These options provide good protection against executable modification. All ICE License information is encrypted and protected in your project resource to reduce the risk of being cracked. MachineID technology to prevent unauthorized copy of your software Machine locking prevents your software from being illegally duplicated and used on other machines. The License can be run on the specified machine only. This protection it's based on CPU, Bios and Hard Disk manufacturer identification. This protection is not based on the getvolume and other routines that require you to send a new license if the user reformats their HDD. Note MachineID result is not warranties. Prevent against illegal license exportation - Unique ! ICE License is the first and only protection which enables you to get total control of licenses using country locking. With this new technique, you can prevent illegal exportation of the LicenseKey. If you create a LicenseKey for a customer located in the United States, other people from around the world cannot use this LicenseKey. Even if a customer tries to deploy or supply the LicenseKey for other people arould the world, the LicenseKey will be not valid. This technique allows you to protect your LicenseKey against illegal warez or serialz websites. Create a key generator for distributor ICE License Protection allows you to create a key generator for your Distributor or Partner to allow them to create licenses for your customers without the need to contact you. Network Protection - control each workstation (TCP/IP protocol) ICE License is designed for networks and allows you to control the number of simultaneous users. It lets you effectively license your application in network environments by controlling the number of software copies that can run at the same time or by assigning the application to specific workstations by Computer ID. ICE License can prohibit the copying of your software from the server hard drive, limit the number of simultaneous workstations, or assign the application to specific workstations by Computer ID. ICE License can limit and lock the number of allowed network users or computers. Features
· Antidebugging & Antimonitors Protection (protect against Code Tracing)
· Sophisticated Asymmetric Encryption Technology (prevent against Key Generator) · Advanced Digital Authentication to prevent against patching · Advanced Code Encryption Protection to prevent against cracking or dumping · Transfer License to another PC (Trial License or Full License) · Create a Key Generator for your partner or distributor · Detects backdating or demo reinstallation to gain additional usage · AES Rijndael Encryption functions to protect your data · Cryptographic hashing MD5 to lock licenses to your software · Machine Locking Protection (when is possible) · Network LAN Control Protection by TCP/IP Protocol (in Trial or Full Mode) · Encrypt & Hide Application Strings to provide a high level of security · Prevent and Control your LicenseKey against illegal exportation - New ! · Using compact LicenseKeys to register with ActiveKey for increased security · Add Extra Information inside License (in Trial or Full Mode) · Restricted Environments (Limited User Mode for NT4, 2000, XP) · View LicenseKey to see details about any License · Create custom URL links to directly access your ordering web page · Invisible software based protection requiring no dongles · Create "Trial Edition" by days, number of uses, hours or a set date · Compatible with Windows 95, 98, Me, NT, 2000, XP. · Support Windows XP SP2 (from ICE License v2.09) · Sources available in Pro Edition only include VCL + ICE Network Server source ICE License actually resists piracy and also prevents the spread of universal cracking methods. Get free fully functional version for evaluation, please go to Download Center borland delphi license control software protection borland delphi c++ builder protection copy protection delphi, software protection delphi, delphi license control, digitals rights, borland delphi protection, shareware protection, delphi lock, native delphi vcl protection |
 Screen Captures  ICE License Manager 
Transfer License Menu 
Network Control Management 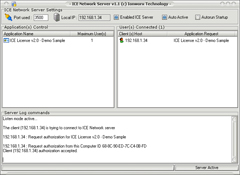
ICE Network Server (Monitoring) 
Distributor Key Generator Management |
|||
| © 2002 - 2014 Ionworx Technology. All Rights Reserved. |
Terms of Usage | Contact Us | Sales Policy |